Removing and Adding Kerberos Authentication within Workspace ONE Access
Introduction:
In this post we will go over both removing Kerberos from Access when using 19.03.xx Connectors and adding in Kerberos Authentication to Workspace ONE Access when using Connector 21.08.xx.
This can be used in conjunction with the Migration to VMware Workspace ONE Access Connector 21.08.xx.
Prerequisites:
- An on-premises 21.08.1 or SaaS Workspace ONE Access tenant
- Workspace ONE Access tenant configured and working
- Workspace ONE Access tenant with a Directory integrated with Active Directory (LDAP or IWA)
- Workspace ONE Access Super Admin login
Documentation:
- VMware Documentation on adding the Kerberos Authentication under Connector Authentication methods.
High Level Process:
- Temporarily "disable" Kerberos in the Access tenant default access policy (remove the Kerberos AuthN).
- Disable Kerberos auth adapter on all 19.03.xx connectors.
- Do the whole connector and directory migration Note: Need to install the 21.08.01 connector prior to/during this process.
- Uninstall the 19.03.xx connectors.
- Then reinstall/modify the 21.08 Connector installation to add in Kerberos.
- "Re-enable" the policy rule in the default access policy (add Kerberos AuthN back).
Process Details:
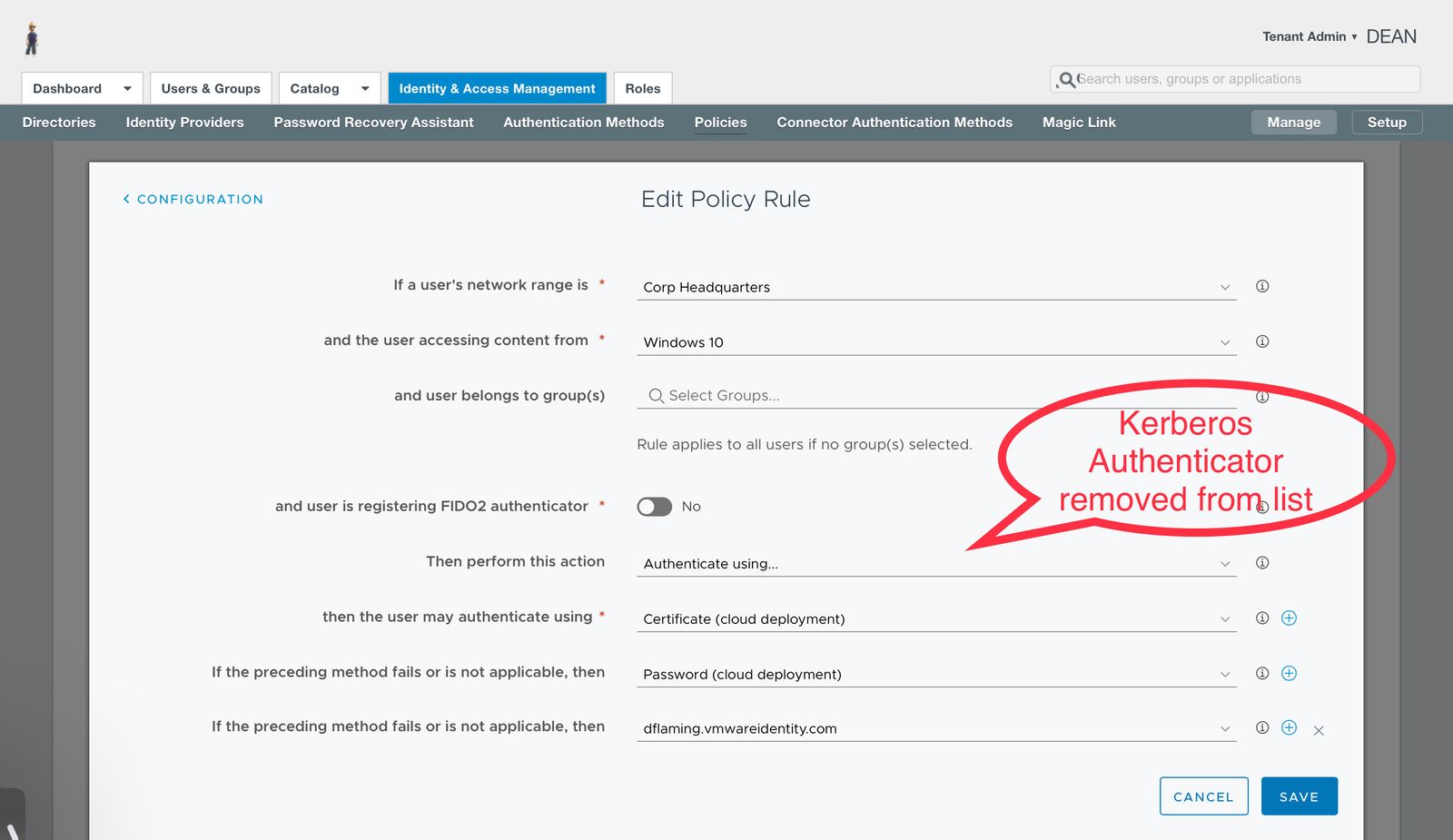
First, edit the Policy Rule which contains the Kerberos Auth adapter, and remove that by setting it to a duplicate of another Auth adapter altogether or a duplicate fallback Auth adapter and saving.
To disable Kerberos on Workspace ONE Access 19.03.xx Connectors, browse to the Workspace ONE Access admin UI and authenticate as a Workspace ONE Access tenant admin if not already there. Once authenticated, navigate to the Identity & Access Management > Setup > Legacy Connectors screen and select one of the connectors and open Authentication Methods. From there, select Kerberos and it should open the Connector UI and allow you to disable the Kerberos authentication for the connector. Do this for all 19.03.xx connectors which you are migrating (assuming this is being done in conjunction with a Connector migration of some sort).
NOTE:
Once connectors are migrated to 21.08.01 (minus the Kerberos service), finish going through the aforementioned blog post and reinstall/reconfigure the 21.08.01 connector and enable the Kerberos Service. You will need to add in server certificates for secure kerberos authentication along with the all of the necessary Root and Intermediate CAs - both for external certificate chains and internal certificate chains such as ADCS configurations which are not naturally trusted.
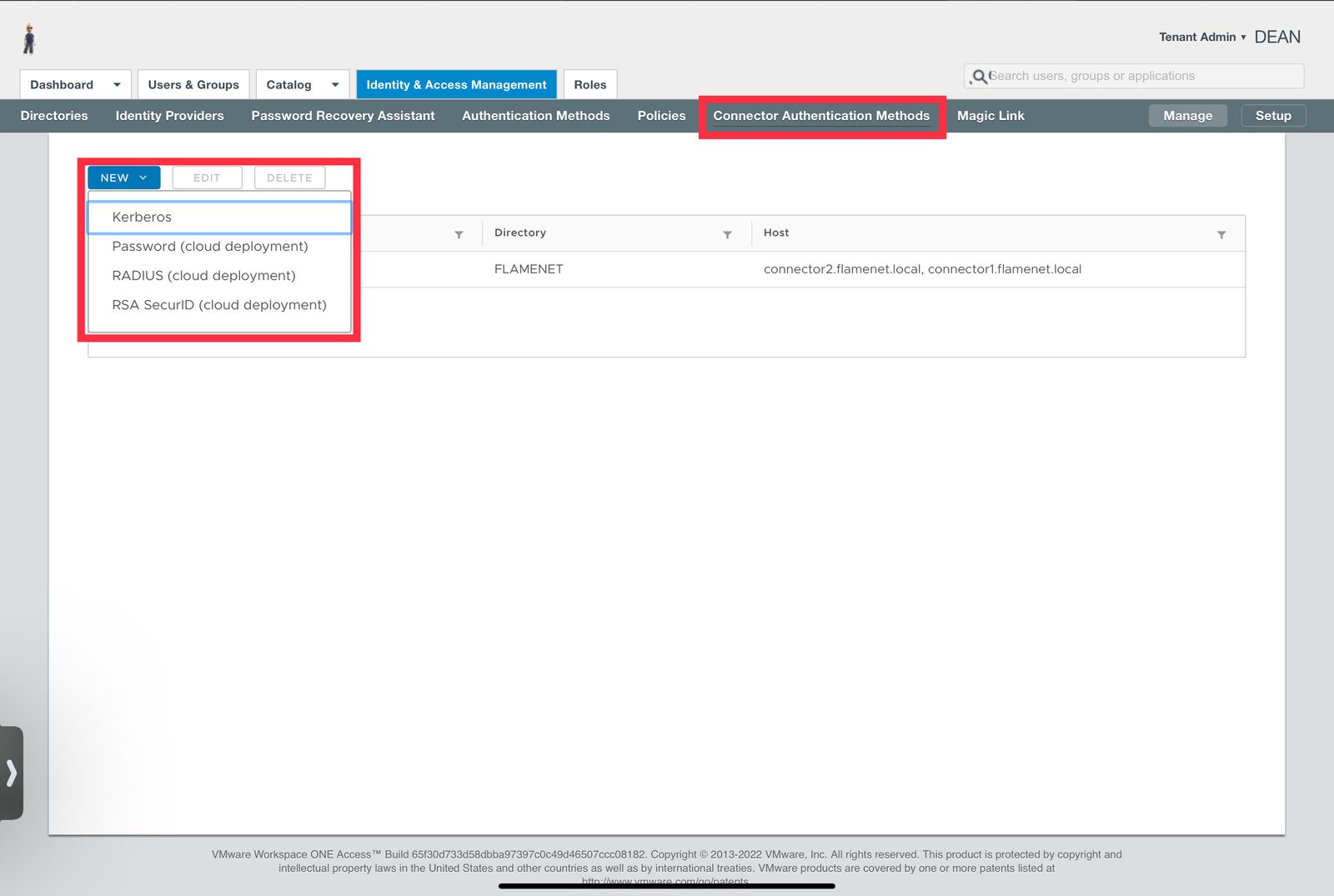
After the 21.08.01 Kerberos services appear on the Connector(s) (see the Connectors status page in the Workspace ONE Access admin console under Identity & Access Management > Setup > Connectors), browse into the admin console and add in the Kerberos authentication under Connector Authentication Methods (See VMW documentation - https://docs.vmware.com/en/VMware-Workspace-ONE-Access/services/ws1_access_authentication_cloud/GUID-6BA53BB4-68D0-463A-AA2E-919F9030CFAA.html)
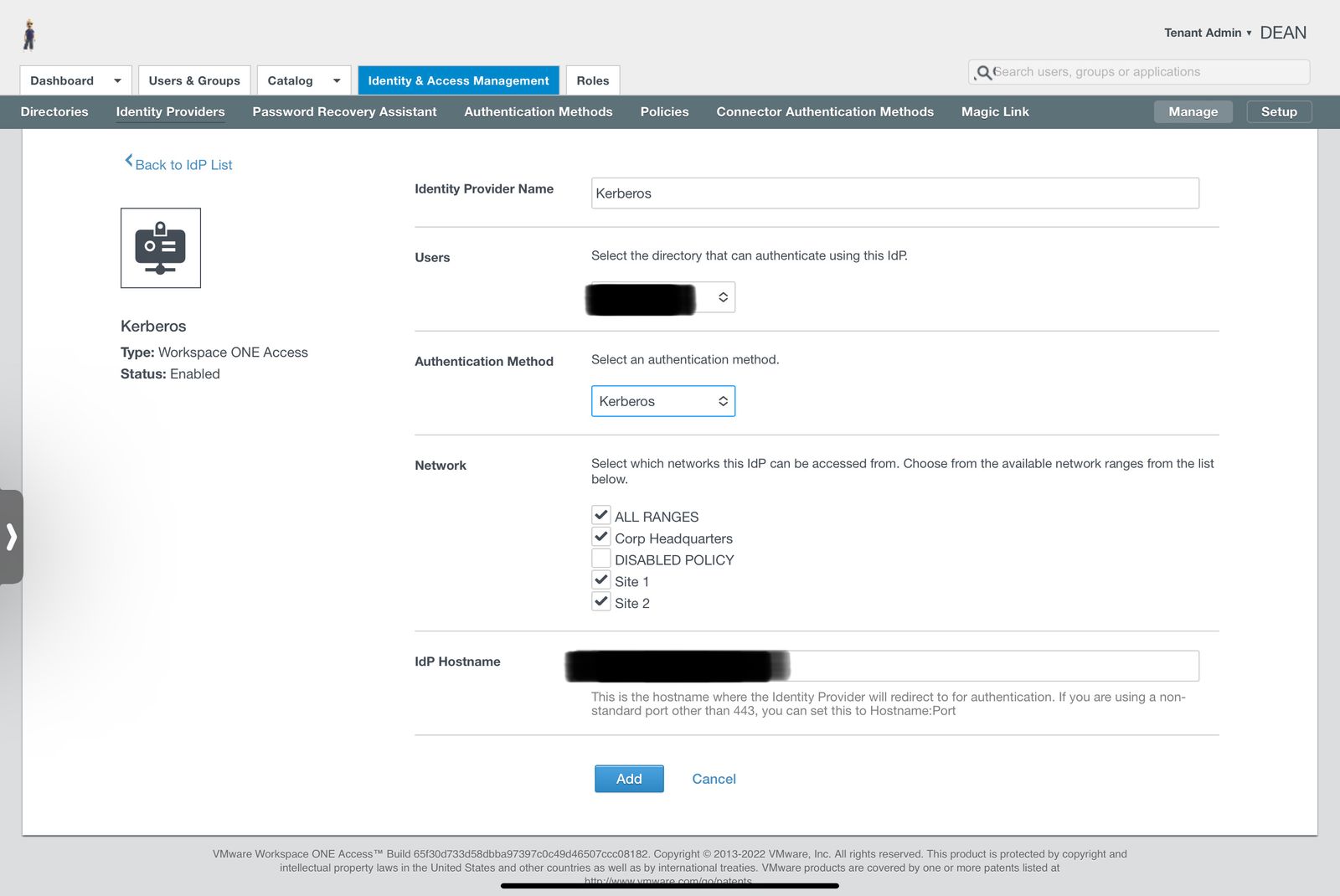
Following Kerberos being created as an Auth source, we must now create a Kerberos authentication adapter (as a Workspace ONE IDP) within the Workspace ONE Access tenant (see VMW documentation - https://docs.vmware.com/en/VMware-Workspace-ONE-Access/services/ws1_access_authentication_cloud/GUID-619D938D-FA99-4494-9EB2-C254B5630EBE.html#GUID-619D938D-FA99-4494-9EB2-C254B5630EBE)
Once that is done, Kerberos can now be added back into the necessary policy rules as an Auth adapter within the default access policy. Simply edit the default access policy set (or other app policy), select the policy rule in question, and edit the policy rule to add in the new Kerberos Auth adapter. Ensure you not only SAVE the policy rule modification, but click NEXT/SAVE on all additional screens within the default access policy or application policy to finish saving it.
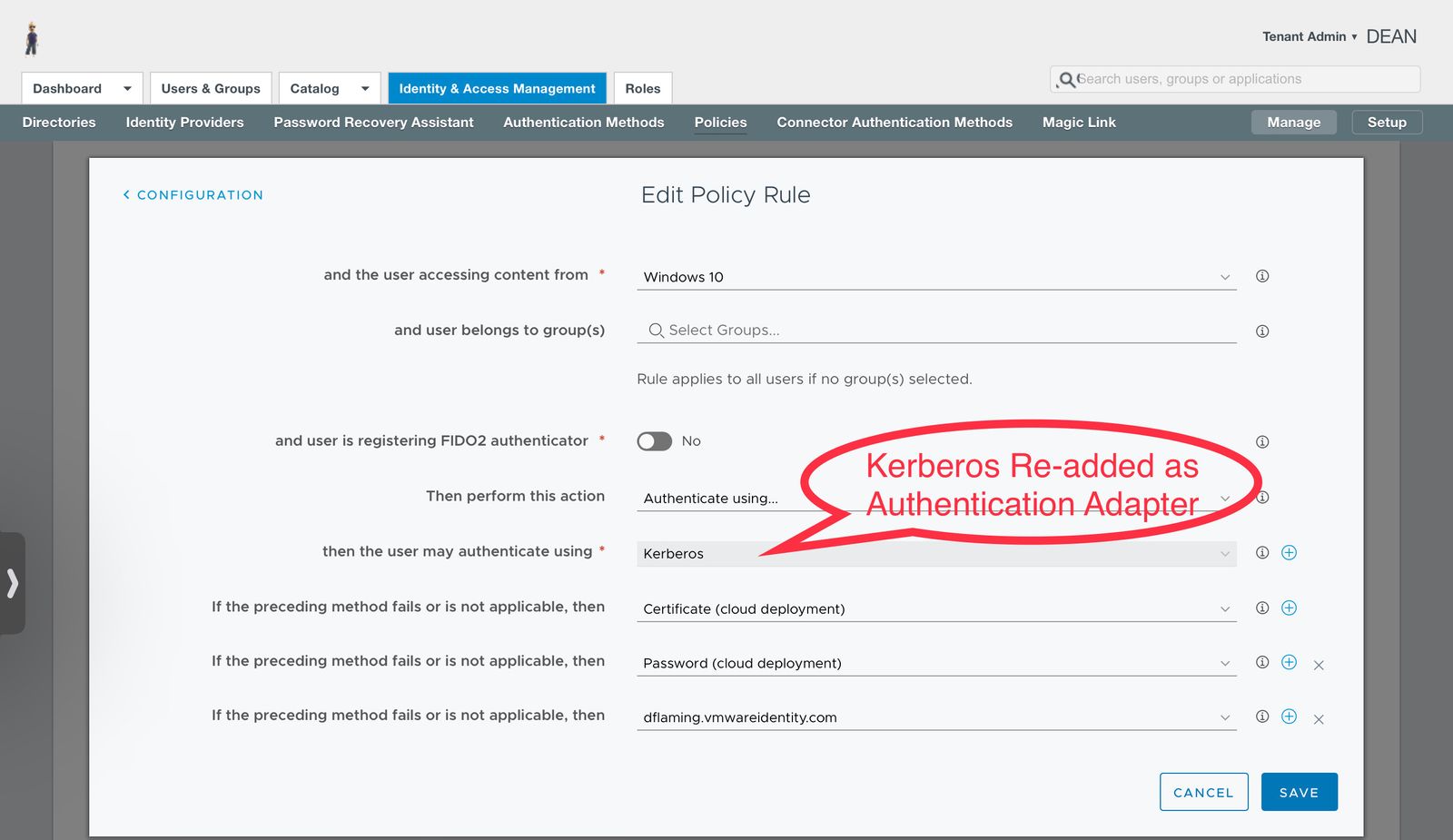
You should now have Kerberos functionally available to all domain joined Windows systems.
The only thing left is to ensure your end point systems properly allow for Kerberos authentication to your Workspace ONE Access tenant. See the VMware Documentation, Configuring Your Browser for Kerberos Authentication in Workspace ONE Access.
